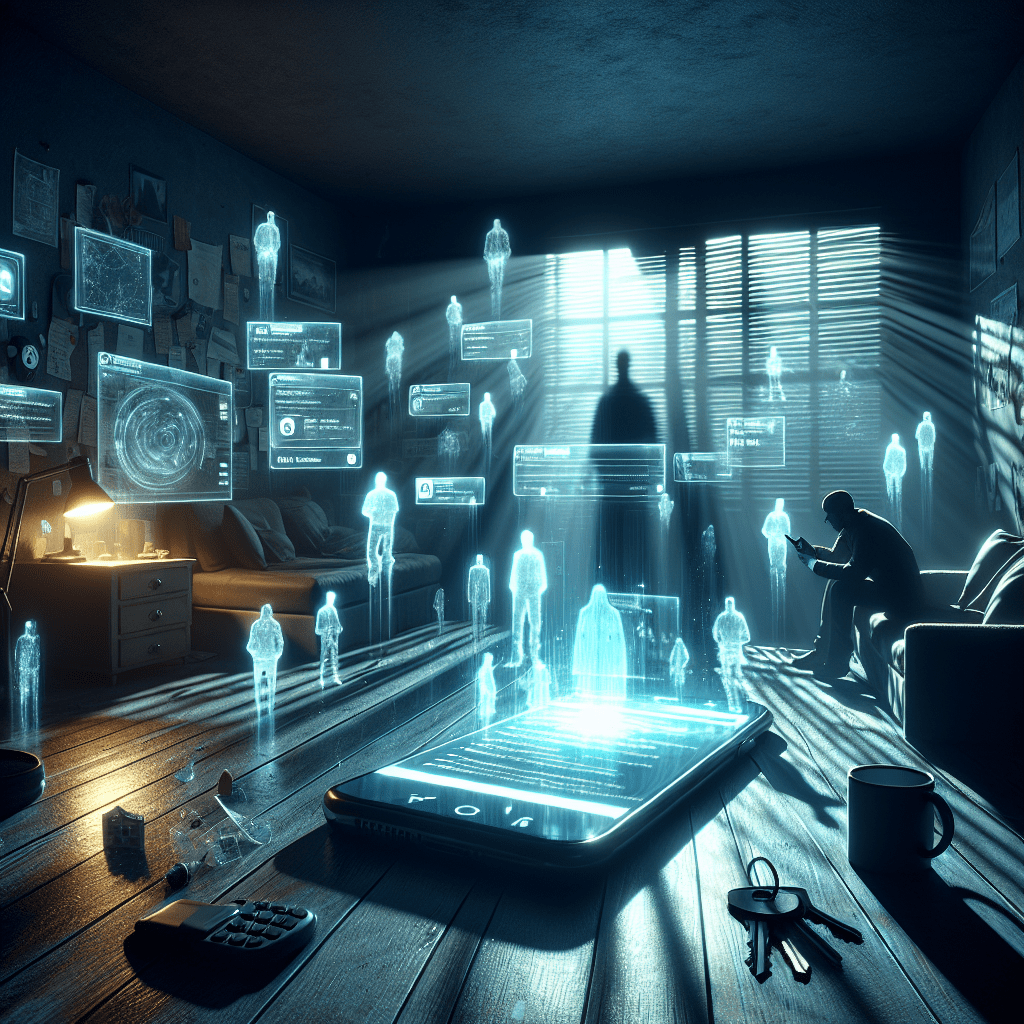
Stalkerware—commercial spyware designed to secretly track someone’s location, messages, calls, and even microphone—has become a powerful tool of digital abuse, often marketed as “parental control” or “partner monitoring” software.
For years, companies profited in a legal gray zone with little consequence. That changed when the U.S. Federal Trade Commission permanently banned Scott Zuckerman, a leading figure in the industry, from ever again selling surveillance apps that operate without the device owner’s knowledge.
This landmark ruling draws a bright line: building and selling software meant to spy on people without consent is no longer tolerable. It serves as a clear warning to the stalkerware industry, its investors, and tech platforms that the era of unchecked covert surveillance is coming to an end.
Background on Stalkerware
Stalkerware sits in a category of its own when it comes to invasive tech. These are apps designed to hide on someone’s phone or computer, tracking their movements, reading their messages, and listening to their calls without them knowing. The software markets itself in different ways, sometimes as a tool for worried parents or suspicious partners, but the reality is far darker. In domestic abuse situations, stalkerware has become a digital weapon, allowing abusers to maintain control long after someone tries to leave.
The apps work by burrowing into a device and operating beneath the surface. They don’t show up in the regular list of installed programs. They send data to someone else, often in real time. Location tracking, text message logs, call records, photos, even audio recordings from the phone’s microphone. The person being monitored has no idea it’s happening, which is precisely the point. Unlike legitimate tracking tools that require consent or at least notification, stalkerware thrives on secrecy.
Smart devices made this problem worse. A decade ago, you needed technical skills to monitor someone’s activities. Now, stalkerware companies package everything into simple downloads with user-friendly dashboards. Some apps advertise on social media. Others pop up in search results when people type in phrases like “how to track my spouse.” The barrier to entry dropped, and the number of victims climbed.
Law enforcement and privacy advocates have been chasing this problem for years, but the technology moves faster than the regulations. By the time one app gets shut down, another appears under a different name. Some operate from countries with weak privacy laws, making them hard to pursue. The companies behind these tools often claim they’re not responsible for how customers use their products, a defense that’s wearing thin as the evidence of harm piles up. International efforts to crack down on stalkerware have gained momentum, but it’s been a game of catch-up from the start.
The FTC’s Decision
The FTC took a hard line here, and the decision deserves attention. After a thorough investigation into how Zuckerman ran his operations, the commission voted to keep him banned from the surveillance software business. The ruling wasn’t close, and it wasn’t ambiguous. This is the kind of enforcement action that makes lawyers for tech startups sit up and pay attention.
What stands out is the message embedded in this decision. Regulatory bodies have spent years trying to figure out how to handle surveillance technology without stifling legitimate security tools or parental monitoring software. The FTC walked that line by focusing on intent and marketing. Zuckerman’s software wasn’t presented as a tool for protecting your kid’s phone usage. It was sold as a way to monitor someone without their knowledge, which crosses into different territory.
The investigation itself took time. Federal agencies don’t move fast, and cases like this involve digging through business records, customer complaints, and the actual code of the software in question. The FTC had to prove that Zuckerman knew what his products were being used for and that he marketed them with that use in mind. They did, and the ban stuck.
This decision creates a precedent. Other developers who operate in the murky space between legitimate monitoring tools and outright spyware now have a clear example of what happens when you lean too far in the wrong direction. The FTC didn’t just slap a fine on Zuckerman and call it a day. They removed him from the industry. That kind of action is rare, and it signals a shift in how seriously privacy violations are being treated at the federal level.
For anyone watching this case, the takeaway is simple. The rules around consumer privacy are tightening, and enforcement is getting sharper. The days of operating in legal gray areas and counting on slow government response are fading. The FTC made its stance clear: if you build software designed to invade someone’s privacy, you will face consequences that go beyond a settlement check.
Scott Zuckerman’s Involvement
Scott Zuckerman built a business around watching people who didn’t know they were being watched. His companies sold software that tracked texts, logged calls, and pinned locations on a map. The apps ran silent. No icons on the home screen, no notifications, nothing to tip off the person carrying the phone. Just data flowing back to whoever installed it.
The tools were marketed with careful language. Parental monitoring. Employee oversight. But the FTC’s investigation painted a different picture. The software ended up in the hands of abusive partners, suspicious spouses, people looking to control rather than protect. Zuckerman’s operations thrived on that ambiguity, selling a product that could be used for legitimate purposes but was often turned toward something darker. The line between monitoring and stalking isn’t always clear, but his software was designed to erase it.
What made Zuckerman’s case notable wasn’t just the technology itself. Plenty of companies dabble in surveillance software. It was the scale and the brazenness. His businesses pushed these apps hard, with affiliate programs and aggressive marketing tactics. They didn’t hide what the software could do. The promotional materials spelled it out: see every message, track every movement, all without the target knowing. The FTC found that Zuckerman’s companies failed to adequately inform users about the legal risks of deploying such software without consent, a requirement that matters when the product you’re selling can land someone in serious legal trouble.
The ban targets not just Zuckerman himself but the practices his businesses represented. By maintaining it, the FTC is making clear that profiting from invasive surveillance carries consequences. The ruling blocks him from selling, promoting, or profiting from any monitoring app that operates without clear and persistent notification to the person being tracked. It’s a direct hit at the core of how stalkerware functions.
- The FTC ruling acts as a strong warning to tech companies that develop or enable invasive surveillance technologies.
- Monitoring software firms are expected to reevaluate their products, with a likely move toward transparent, consent-based design or exiting the market.
- The financial and reputational risks associated with stalkerware now extend to investors, influencing venture capital scrutiny.
- Global regulatory trends are aligning with the FTC’s stance, creating a challenging environment for companies operating internationally.
- The industry may gradually embrace privacy-by-design principles, but enforcement actions are likely to be the main driver of change.
| Key Implication | Description |
|---|---|
| Industry Warning | FTC sets precedent discouraging surveillance tech misuse |
| Product Redesign or Exit | Companies must adopt transparency or leave the market |
| Investment Risk | Investors face reputational and financial risks from backing such tech |
| Global Regulatory Convergence | Increased international enforcement against invasive monitoring tools |
| Shift Toward Privacy-by-Design | Enforcement likely to push industry toward stronger privacy protections |
Consumer Awareness and Protection
The FTC’s decision against Zuckerman puts a spotlight on something most people don’t think about until it’s too late: the fact that someone could be watching everything you do on your phone. Stalkerware sits there in the background, invisible, collecting texts, photos, location data, even recording calls. It’s the digital equivalent of having someone rifle through your diary every night while you sleep.
The tricky part is that victims often have no idea they’re being monitored. The software is designed to hide itself, no icon on the home screen, no suspicious battery drain, nothing that screams “something’s wrong here.” By the time someone discovers they’ve been tracked, months or even years of private information might have been compromised. That’s what makes awareness so critical. People need to know what signs to look for: unexpected permission changes on apps, data usage that doesn’t match their habits, or a partner who seems to know things they shouldn’t.
Security experts recommend a few basic steps that can help. Keep your phone’s operating system updated, since patches often close vulnerabilities that stalkerware exploits. Use strong passwords or biometric locks, and don’t share them with anyone, even people you trust. If you suspect something’s off, a factory reset can wipe out hidden software, though it’s worth consulting with a domestic violence organization first if you’re in a dangerous situation. They can help you plan safely.
Privacy advocacy groups have been pushing for better public education on these issues for years. Organizations like the Coalition Against Stalkerware work with antivirus companies to detect and remove these apps, but they’re fighting an uphill battle. The technology moves faster than public awareness does. What helps is when regulatory bodies like the FTC take visible action. Cases like Zuckerman’s generate headlines, which gets people talking, which spreads information to those who need it most.
There’s also a role for tech platforms here. App stores could do more to vet software before it goes live, flagging apps with suspicious permissions or vague descriptions. Some companies have started cracking down, but enforcement remains inconsistent. Google and Apple have policies against stalkerware, yet apps still slip through, often marketed as parental control tools or employee monitoring software. The line between legitimate use and abuse gets murky fast, and that ambiguity creates cover for bad actors.
The bottom line is that people need to take their digital privacy as serious as they would their physical security. Lock your phone like you’d lock your front door. Pay attention to who has access to your devices and what apps are running on them. And if something feels wrong, trust that instinct. The FTC’s action against Zuckerman won’t stop every stalkerware operation out there, but it’s a start. The rest comes down to individual vigilance and a culture that takes privacy violations as the serious threat they are.
Consumer Awareness and Protection
In light of the FTC’s decision, there is a heightened need for consumer awareness regarding stalkerware and its implications. Educating the public about digital privacy risks is essential for protection against unwanted surveillance.
- Awareness campaigns could help inform individuals about the potential risks and signs of stalkerware.
- Encouraging the use of protective measures, such as installing security software and regularly updating devices, can enhance personal security.
- Collaboration between regulatory bodies and advocacy groups is vital in building comprehensive educational resources for consumers.
Here’s the thing about stalkerware: most people don’t even know it exists until it’s too late. The FTC’s ruling against Zuckerman matters, but only if people understand what they’re up against. These apps don’t announce themselves with pop-ups or notifications. They sit quiet in the background, logging every text message, every phone call, every place you visit. Your phone feels normal. Everything looks normal. That’s the whole point.
The challenge runs deeper than just technical knowledge. Domestic violence advocates have been sounding the alarm for years about how stalkerware gets weaponized in abusive relationships. Someone gets access to your phone for a few minutes, installs an app disguised as something harmless, and suddenly they have a window into your entire life. The power imbalance this creates is staggering. It’s not just about privacy in the abstract sense. It’s about safety, autonomy, and the ability to leave a dangerous situation without being tracked.
So what can people do? Start with the basics. If your phone battery drains faster than usual, or it gets hot when you’re not using it, that could be a red flag. Random shutdowns, weird background noises during calls, or data usage that doesn’t match your habits are all worth investigating. Security researchers suggest running regular scans with reputable anti-spyware tools, but here’s where it gets tricky: some stalkerware is sophisticated enough to hide from detection software. The apps often have innocuous names like “System Service” or “Device Health.” They blend in.
Tech companies have started stepping up. Apple and Google have implemented features that make it harder to sideload suspicious apps, and both have tightened permissions around location tracking and microphone access. But the cat-and-mouse game continues. Developers find workarounds. New exploits emerge. The regulatory framework struggles to keep pace with the technology itself.
Advocacy groups and organizations like the National Network to End Domestic Violence have developed practical resources for people who suspect surveillance. They recommend doing sensitive activities, like researching escape plans or contacting support services, on a device the potential abuser has never touched. A work computer, a friend’s phone, or a public library terminal becomes a lifeline. Factory resetting your personal device might seem extreme, but it’s one of the few reliable ways to remove stalkerware if you can’t identify the specific app.
The FTC’s action against Zuckerman sends a message, but enforcement alone won’t solve this. People need to know these tools exist, how they work, and where to turn for help. Schools could integrate digital privacy into their curricula. Healthcare providers who work with abuse survivors could screen for stalkerware as part of their safety planning. Wireless carriers could offer educational materials when people sign up for service. The infrastructure for awareness exists. It just needs to be activated and funded properly.
This post contains affiliate links. If you purchase through these links, I may earn a commission at no extra cost to you.
Leave a Reply to xAI Expands AI Reach with Video Tech – Thoughts on TechnologyCancel reply